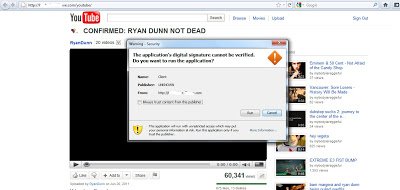
The page is designed to mimic the YouTube service. If however you inspect the source code of this page, you can identify the malicious binary behind this attack. Here is what the source code looks like:
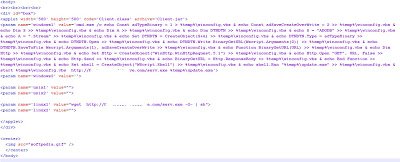
The webpage includes a Java applet that runs a “YouTube.jar” file, which will then download “ser.exe” from the server. If you visit the homepage of above site, you will also see a separate Java applet being combined with VBScript to download and run the same malicious binary with a slightly different name “serv.exe”, which will later saved as “update.exe”. Here is screenshot of that script:
While the malicious files are currently detected by some antivirus products, the malicious website is not blocked by Google Safe Browsing. It is never advisable to download or run any executable from an untrusted source unfortunately, this relatively simple social engineering technique clearly still works.
Umesh